The Power of the Routing Table in Computer Networking
In today’s world, we cannot do much without being connected to the Internet. It is through the Internet that we can reach out to our loved ones, learn new things, grow businesses, and much more. But the Internet itself was developed as a network of networks, which means that understanding the basics of computer networking is very important, especially if we want to delve into the software and IT industries.
Computer networking includes many important concepts, tools, and algorithms through which are combined to connect two or more computers and enable them to communicate using network packets.
Let’s consider two computer systems A and B. If A and B want to send network packets to each other, then there are some basic requirements for this:
- A and B must have wired and/or wireless connectivity. This does not necessarily mean that they must have a direct connection between them. It can be through different network devices as well.
- A and B must have at least 1 IP address allocated to their NIC (Network Interface Card)
- A and B must be connected by a switch if they are in the same network, or by a router if they are present in different networks.
But even with these requirements, A and B must have other configurations set up to allow communication between them. Every computer communicates with other computers based on a list of rules. These rules decide which computers can the local host send/receive network packets. These rules are given in the table called the routing table.
This means if we can modify the rules written in the routing table, we can control the network traffic between the local host and computers in the same or different networks.
Let’s test this out, by adjusting the routing table rules so that we can ping Google, but not Facebook. The following commands are being run on an RHEL8 VM running on Oracle Virtual Box with the host system using Windows 10.
Let’s Block Facebook but not Google
To see the routing table in Linux, we use the route command, which is installed as a part of net-tools. If you do not have net-tools installed in your distribution, you cannot use the route command.
The route command allows us to work with the IP routing table. To understand more about its working, it is best to check the man pages of the command itself.
Firstly, we can see the configured routing table using the route -n command. It is best to always see the existing routing rules before we make any changes. The option -n displays the routing table entries in full numeric form (IPv4 addresses). Sample output is shown below.
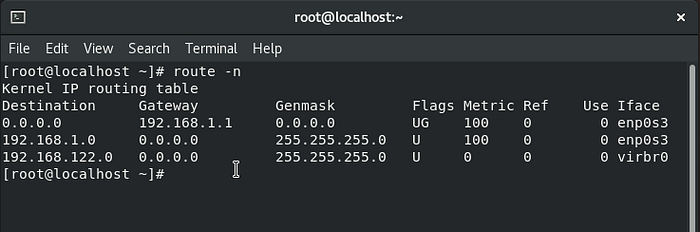
route -n commandLet’s try to understand the information given in the routing table.
- The Destination column shows either a subnet ID or a single host IP Address. But how do we figure out if the given IP address refers to a single host or many hosts belonging to one subnet? To differentiate between the two possibilities, we use the Genmask (Netmask) column. The columns Destination and Genmask (Netmask) work together to lay down rules to decide which IP addresses can receive packets from the localhost. We cannot decide the possible destination IP address or range of IP addresses (for a subnet) only by referring to the Destination column. We need to take the netmask also into account. Let’s consider the first entry of the table. Destination 0.0.0.0 and Genmask(Netmask) 0.0.0.0 refers to a range encompassing all IP addresses. Simply put, it means any IP address. Typically, the netmask for the destination net is 255.255.255.255 for a host destination and 0.0.0.0 for the default route (to any IP Address).
- The Gateway column refers to the IP address through which the network packets will be sent to the allowed destination(s). For the first entry, the Gateway is the default gateway for the computer (192.168.1.1).
- The Iface (Interface) column refers to the Network Interface Card (NIC) through which the network traffic for a particular destination subnet will be routed.
- The Flags column lets us understand more about the route to a destination. It can have different values. In the image above, we see two values U and G. U signifies that the route is up, while G signifies that the destination is reached by passing through the Gateway. You can read more about the other values for flags here.
- The Metric column shows the number of hops a packet has to make to reach the destination subnet via the gateway.
- The Ref column indicates the number of references to this route.
Based on the rules currently set up in the routing table, we will be able to connect to any IP Address in the world. We can test this out by using the ping command.
Now, we modify the routing table such that it cannot ping any IP in the world (not even in its own subnet). To achieve this, all we need to do is delete the rule which allows Destination 0.0.0.0 network traffic through the default gateway.
Before deleting this rule, make sure that you have the IP addresses that connect you to Google and Facebook. To find these IP addresses, we can use the nslookup command.
nslookup www.google.com -> To find the IP address of www.google.com
nslookup www.facebook.com -> To find the IP address of www.facebook.com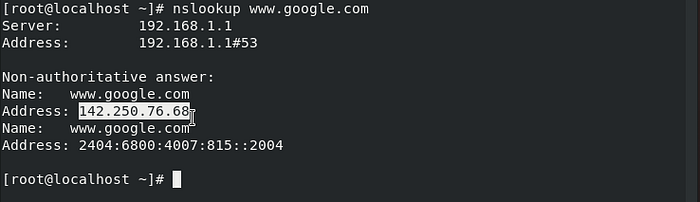

Keep note of these addresses, as we will be using them later. Now, we delete the desired rule from the routing table using the following command
route del -net 0.0.0.0 enp0s3After this command is executed, we can see the changes in the routing table.
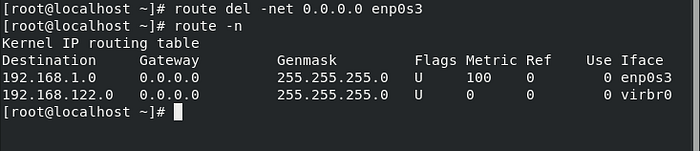
Now, if we try pinging any generic website, like Google, or Yahoo, we will not be able to do so.

Now, our motive is to create a rule so that we can ping only Google but not Facebook. This means we need to lay out a new route for one of the IP addresses through which we can access Google (we just found one a little while ago!). We have two options now for creating the route — either add the rule for a singular host, or for an entire subnet to which the Google IP address can belong. For now, we will go with the second option and set a random netmask (like 255.255.255.0), and set the route such that it passes through the default gateway. We can add the new rule using the following command
route add -net 142.250.76.0 netmask 255.255.255.0 gw 192.168.1.1 enp0s3Now, the routing table is as shown below.
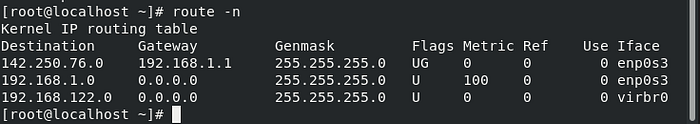
Now let’s trying pinging Google!
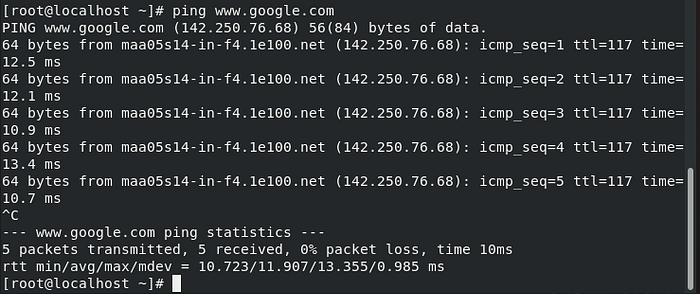
Now, we verify if our rule really works by trying to ping Facebook!
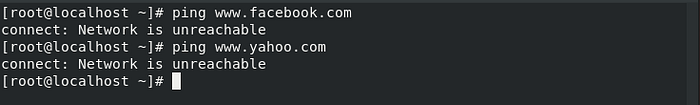
We can see that we are only able to ping Google, and not any other website or IP address.
Now we have created our own rules for the routing table! But how do we go back to the original settings??
It’s very simple! You only need to switch off and then switch on the network connection on your device.
Selectively allow traffic for your computer within your subnet
Let’s try another fun exercise, where we want to set up rules for 3 computers A, B, and C. Our objective is to allow A to communicate with B and C. At the same time, B and C can only communicate with A and not with each other. The set up is based on the diagram shown below.

We find the IP addresses and netmasks of the 3 computers (or VMs) we will be using from the following command
ifconfigA — IP=192.168.1.55, netmask=255.255.255.0
B — IP=192.168.1.58,netmask=255.255.255.0
C — IP=192.168.1.59,netmask=255.255.255.0
From the IP addresses and netmasks, we can say that all 3 computers belong to the same subnet, and they also share the same default gateway (192.168.1.1).
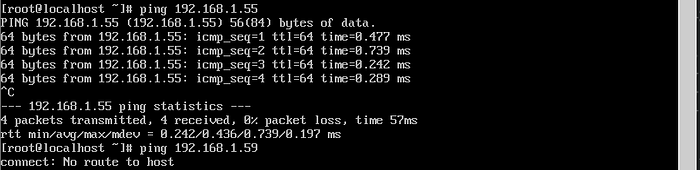
A simple way to prevent B and C from pinging each other is to use the reject option in the route add -host subcommand. By adding the reject option, we are preventing the tracking of a route to the mentioned host. The command is as shown below.
route add -host <IP address of host> rejectOnce the route has been rejected we see the following changes in the routing tables of computers B and C.

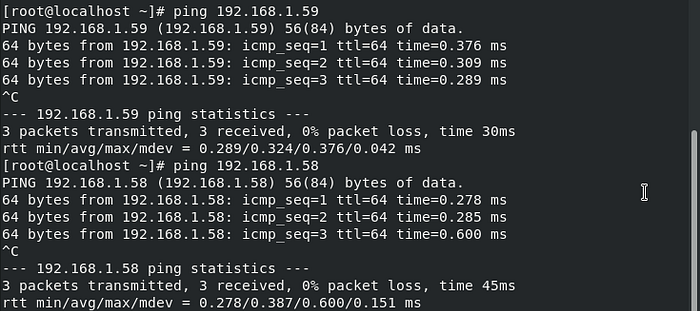
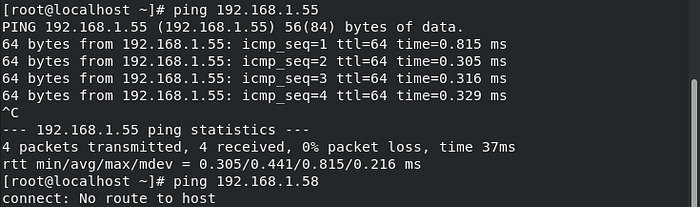
Now, if we try pinging A from B and C, the ping command works successfully. But if we try to ping B from C or C from B, the ping command fails since there is no route for the network packets to travel through.
Conclusion
Understanding routing tables and how the rules in routing tables function are very important to set up computer networks from scratch. The two examples in this article show only a part of what we can really accomplish with the routing table and its rules.
